The Apple Security Research Device program launched today, and it aims to provide special iPhones to researchers with code execution and containment policies.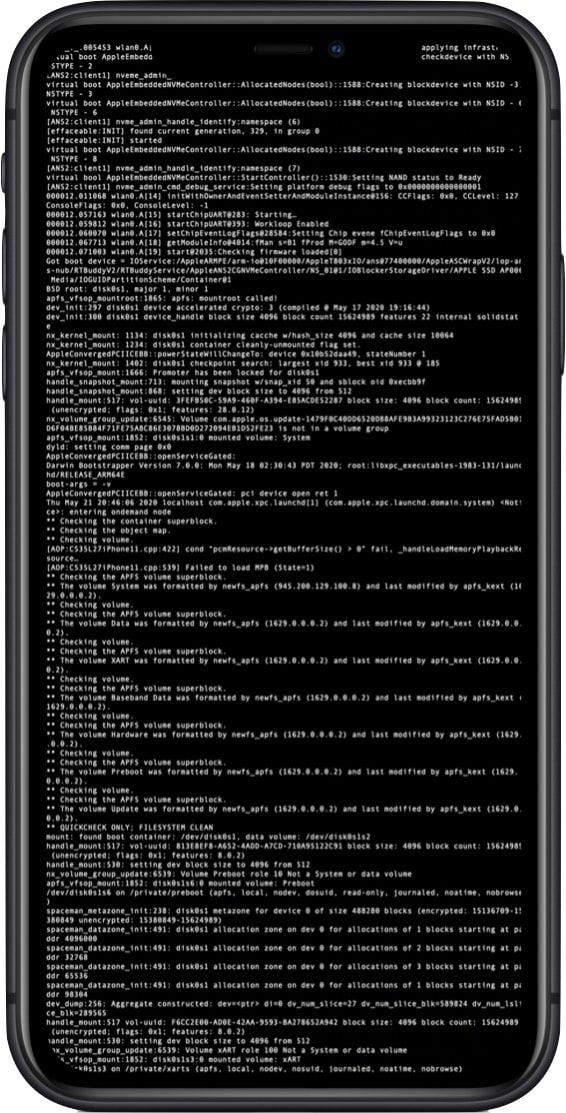
Apple Security Research Device Program
The Security Research Device (SRD) will have shell access available to run any tools and entitlements. They remain Apple’s property but can be leased on a 12-month basis. Here are the program’s restrictions:
- If you use the SRD to find, test, validate, verify, or confirm a vulnerability, you must promptly report it to Apple and, if the bug is in third-party code, to the appropriate third party. If you didn’t use the SRD for any aspect of your work with a vulnerability, Apple strongly encourages (and rewards, through the Apple Security Bounty) that you report the vulnerability, but you are not required to do so.
- If you report a vulnerability affecting Apple products, Apple will provide you with a publication date (usually the date on which Apple releases the update to resolve the issue). Apple will work in good faith to resolve each vulnerability as soon as practical. Until the publication date, you cannot discuss the vulnerability with others.
Applicants also have to meet requirements like having a proven track record of finding security issues, and have an Apple Developer membership.
